The ExtraHop Reveal(x) Platform Offers Critical Monitoring
Instead of working with agents that would need to be installed on devices, ExtraHop Reveal(x) pulls in raw network traffic from a variety of potential sources, including network taps or port monitors. For Amazon Web Services or Microsoft Azure clouds, it can read all the data coming from a virtual traffic mirroring feed. It then analyzes that traffic — and can do so very quickly at up to 100 gigabytes per second.
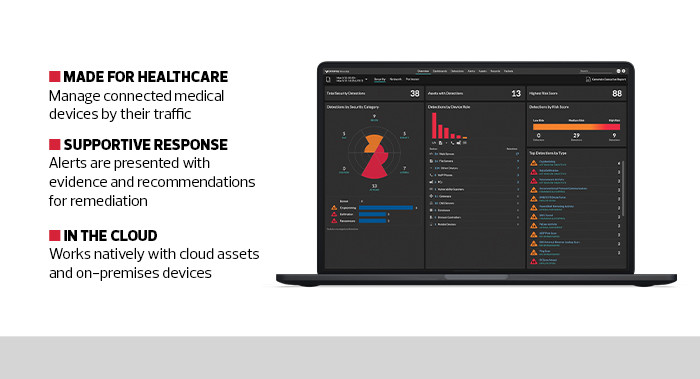
The platform then begins to classify every device operating on the network using its highly trained machine learning engine. In testing, it properly discovered everything from a Domain Name System server to a heart monitor. Reveal(x) comes pretrained so that it can quickly identify thousands of medical and Internet of Things devices. It can also learn about new or unique devices that may be operating within a healthcare network.
Once identified, devices are put into logical groups so that Reveal(x) can monitor traffic to determine what normal patterns flow within the network to compare against future outliers. It can also immediately identify malicious traffic associated with cryptomining or attack patterns.
The network discovery process is not a one-time event: Reveal(x) is always monitoring traffic, so every time a new device comes online, it will be identified the instant it starts to communicate. In this way, the platform can quickly identify and protect newly installed equipment; it can also reveal shadow IT or unauthorized devices before they can touch any other network assets.